What We Do
Most businesses only discover their security gaps after an attack. We find them first.
Strategy, governance, and leadership - built around your risk.
Expert-led programmes that align your security investment with your business objectives. No off-the-shelf solutions. No unnecessary complexity.

Organisational Cyber Maturity Assessment
You can't fix what you don't measure. We benchmark your security posture against real-world threats and give you a clear, prioritised roadmap - not a report that gathers dust.
Learn More
Risk Management
Not all risks deserve your budget. We identify what's actually threatening your business and help you invest where it matters — so you stop guessing and start deciding with confidence.
Learn More
Regulatory Compliance
GDPR. ISO 27001. 27701. SOC2. CRA. NIS2. The regulations aren't slowing down. We get you compliant, keep you compliant, and make sure compliance becomes a competitive advantage - not a cost centre.
Learn More
vCISO
Enterprise-grade security leadership without the enterprise price tag. Your dedicated vCISO owns the strategy, drives the programme, and sits at the table with your leadership team when it matters most.
Learn MoreRelentless sentry. Built for when it can't go wrong.
For organisations where a breach isn't just costly - it's existential. Symmetry Black delivers dedicated, always-on intelligence at the highest level of protection.
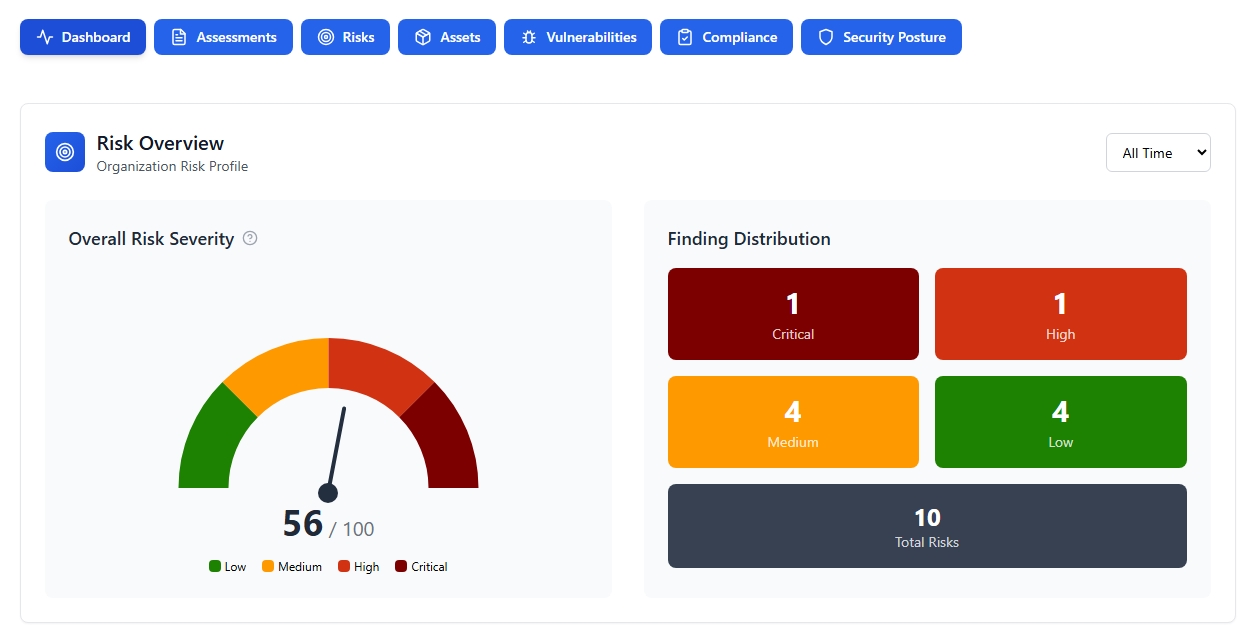
Cyber Security Posture Management
Continuous, asset intelligence-led posture visibility across your entire attack surface that enumarates your cloud and endpoint asset risk. Not a point-in-time snapshot. A living, breathing view of your exposure, updated as your environment evolves.
Explore Symmetry Black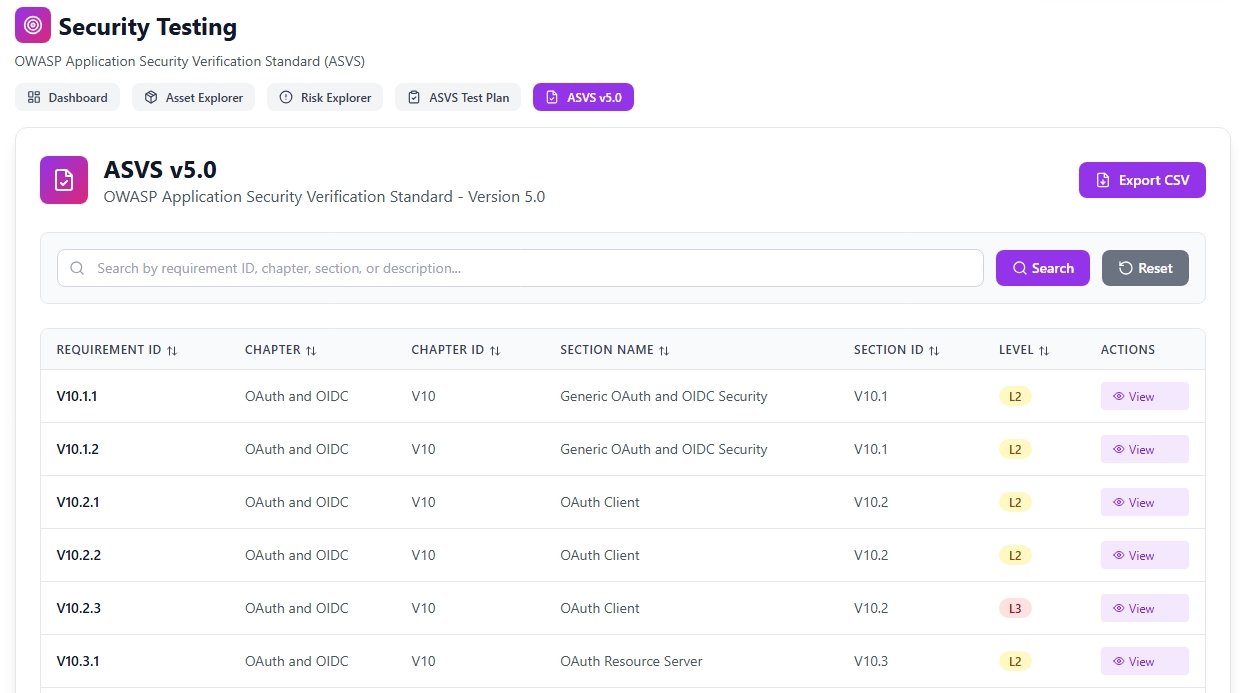
Dynamic Application Penetration Testing
Real attackers don't follow a checklist. Our OWASP ASVS Level 1 application penetration test goes beyond automated scanning to expose the vulnerabilities your developers didn't know were there. On demand. But most of all, before someone else finds them.
Explore Symmetry Black
AI Managed Detection & Response (Coming soon)
Threats move in milliseconds. Your response has to match. Our AI-powered MDR layer monitors, detects, and acts 24/7 — stopping breaches before your team even gets the alert.
Explore Symmetry BlackA disciplined approach to every security problem
Discover
Understand your business model, architecture, data flows, risk and gaps via a thorough organisational assessment.
Design
Develop a tailored security strategy, realistically aligned with your current resource capacity, business objectives and growth plans.
Deliver
Work with stakeholders to implement solutions with minimal disruption, while transfering knowledge to help you scale your internal capability.
Evolve
Continuously monitor drift, adapt, and improve your security posture with our AI platforms as threats and your business evolve.
Ready to get started? We can help.
Find out what's exposed before someone else does. Black Box Posture Assessment - no agents, no access, no excuses.
CONTACT USNo commitment required ·